Joe Sandbox 38 Ammolite
Published on: 15.10.2023
Today, we are proud to release Joe Sandbox 38 under the code name Ammolite! This release is packed with many new detection signatures and important features to make Joe Sandbox even better.
If you wish to upgrade your on-premise Joe Sandbox installation right away, please read the Update Guide that you received via our e-mailing list. You can also find the Update Guide in our customer portal.
334 new Signatures
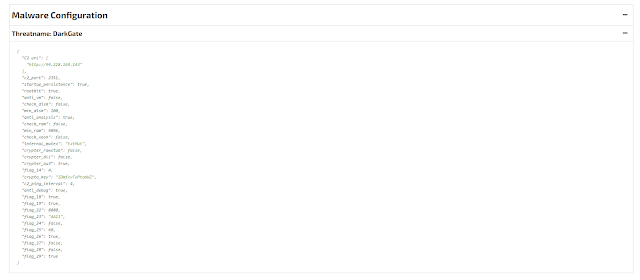
Ammolite comes with a high number of new Yara and Behavior signatures to detect new malware families like RustBucket, AMOS Stealer, Realst, CamaroDragon, Evil Minio, Mystic Stealer, KnightCrypt, Payola, NoEscapeLocker, Purecrypter, DwnedCrypt, Poverty Stealer, RATRUN Stealer, VeDich Stealer, Tigon Stealer, Phemedrone Stealer, Anthrax Stealer and Muggle Stealer and many more. In addition, we added over 18 new Malware Configuration Extractors, e.g. DarkGate, Poverty Stealer, Mystic Stealer, ConnectBack, Customer Loader, Blank Grabber to name a few:
macOS Ventura on Apple Silicon (ARM64)
Ammolite is to our best knowledge the first dynamic analysis system/sandbox that supports macOS Ventura running on Apple Silicon (ARM64) native analyzers. Ammolite is equipped with a brand new introspection technology which provides extremely good performance. Hence, Live Interaction is very fluid and fast, making interactive analysis very convenient to work with.
EML / MSG / JS / ZIP Parser
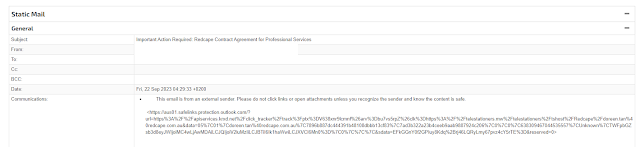
Analysts can upload over 5,000 different file formats to Joe Sandbox for analysis. Saved email formats such as EML and MSG (Outlook) are supported, too. Ammolite brings a new file parser for emails as well as JavaScript and ZIP files. This enables Joe Sandbox to provide more in-depth analysis and detections. Below you find an excerpt of the analysis report for an MSG analysis. Thanks to the MSG parser embedded images are extracted and detected by the phishing engine:
Analysis Report: https://www.joesandbox.com/analysis/1312727/0/html
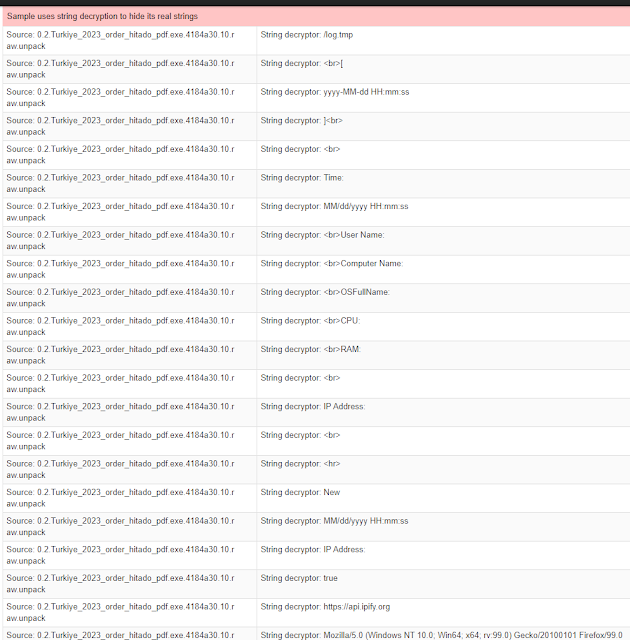
String Decryptors
Besides packing, many malware samples use string encryption to hinder static analysis. However, malware strings are the bread and butter for most analysts. Hence Joe Sandbox Ammolite includes 20 different string decryptors. Analyst can access all decrypted strings from the report:
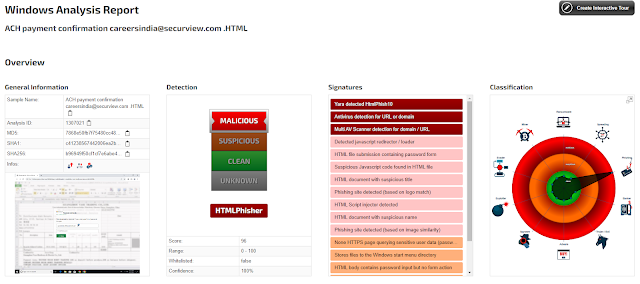
HTML Phishing and Smuggling Detection
Payloads hidden in HTML, HTM, XHTML, SHTML, etc. files continue to be a huge trend. Ammolite has extended capabilities to detect such attacks. This includes new behavior signature, additional modules for dynamic extraction, and static rules:
Analysis Report: https://www.joesandbox.com/analysis/1307021/0/html
Quishing (QR Code Phishing) Detection and Automation
QR codes become a major trend to lure victims. Ammolite detects QR codes, decodes them, and launches embedded payloads fully automated. Analysts can submit an image (PNG, JPEG, GIF, etc.), PDFs, Word documents, EML / MSG etc.
Analysis Overview Redesign
The analysis overview is a key part of the Joe Sandbox Web interface. It lists all finished and previous analysis results. Ammolite includes a brand new design for the analysis overview which greatly improves the usability. With one click analysts can open the full analysis report, the executive report, or the IOC report. Also, the visibility and usability of the analysis detail page have been improved.
Final Words
In this blog post, we have presented the most important features of Joe Sandbox Ammolite, but there are some other interesting features on top:
- Added support for Windows 10/11 22H2
- Added OneNote link analysis
- Added phishing detection for SVGs
- Added detection for COM Dll loading
- Added memory dump information to Linux and Mac reports
- Added Yara scanning for Android memory strings
- Added programming language detection for Rust and GoLang
- Improved performance and filtering of memory dumping
- Improved .Net decompilation (ILSpy)
- Improved precision of phishing detection with a CNN
- Improved analysis of corrupt APK (zip header) files
- Improved DMG file detection
- Improved DMG file static analysis
- Improved VBS script start
- Improved network noise filtering
- Improved Chrome download automation
Would you like to try Joe Sandbox? Register for a free account on Joe Sandbox Cloud Basic or contact us for an in-depth technical demo!